Gadgets
You can’t miss these 10 ways to track your Android mobile phones.
Here we can list out the top 10 ways to track your Android Mobile Phones by using the web and mobile apps. it possible to track you’re lost, stolen phones.

Are you one of those people who use their phone to play free survival games. and can’t miss a day without playing them. Imagine yourself if you lose your phone for even a single day. So, this is a must needed blog for you. As today I am going to tell you different ways to track your android mobile phones.
In today’s scenario technology has been gone to an almost next level and made it possible to track your lost, stolen or misplaced Android devices. This can be done by using software, spy app etc. these things provide help towards reaching your goal.
Table of Contents
1. Find My Device
Every android phone comes with Find My Device service. This can help you in tough times when you are unable to locate your phone just open your laptop or any smartphone and by the help of Find My Device you can easily get the last location of your device.
Also, it enables you to ring your phone or make it locked. Still unable to find that on your android phone. So here is a quick guide on how to activate on your android phone.
1. Open settings option
2. Tap on the security option
3. Select Device administration option
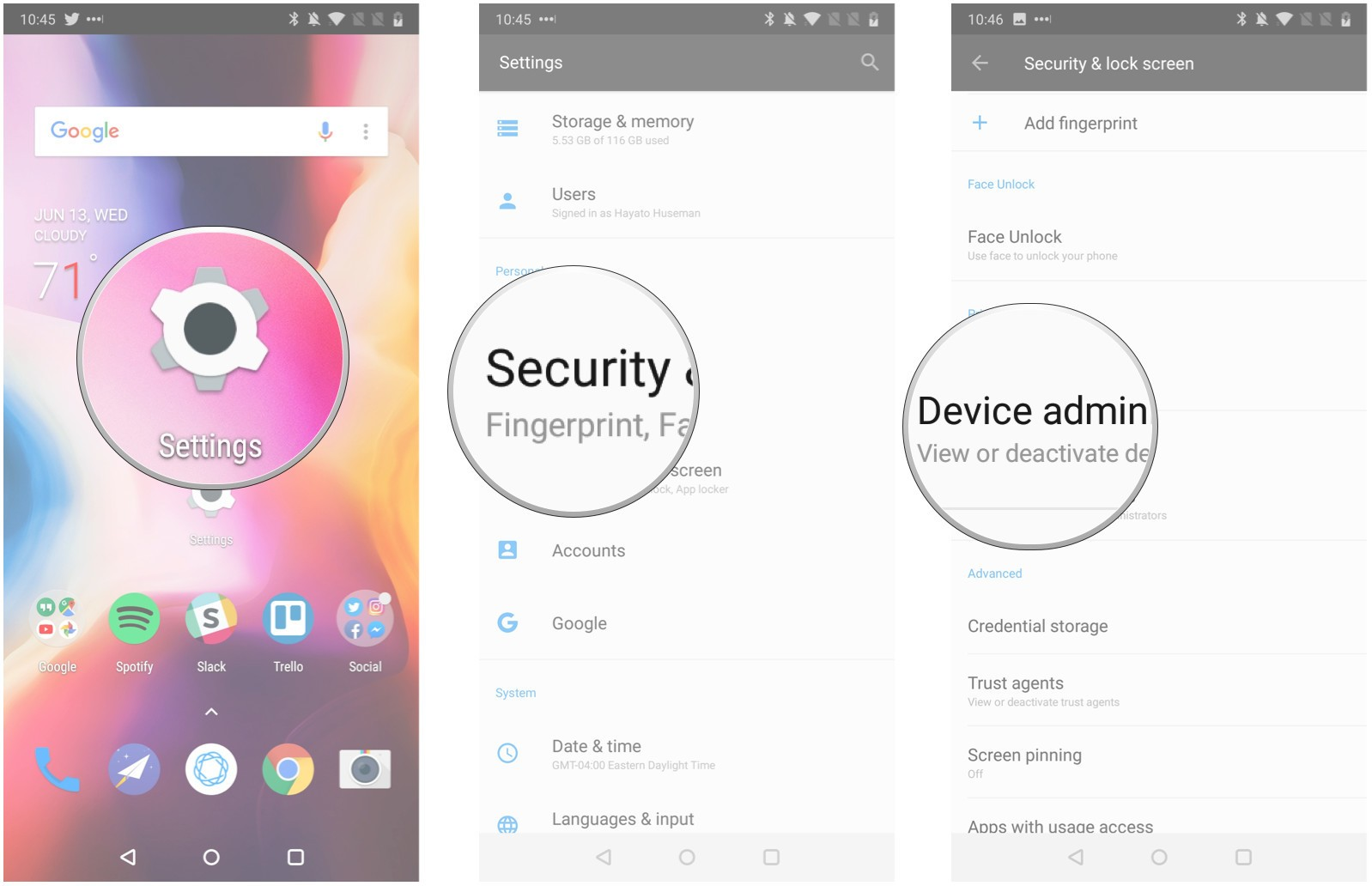
4. Click on Find My Device option
5. Check top left corner of your mobile screen and tap on the back option
6. Click on Location in setting menu bar
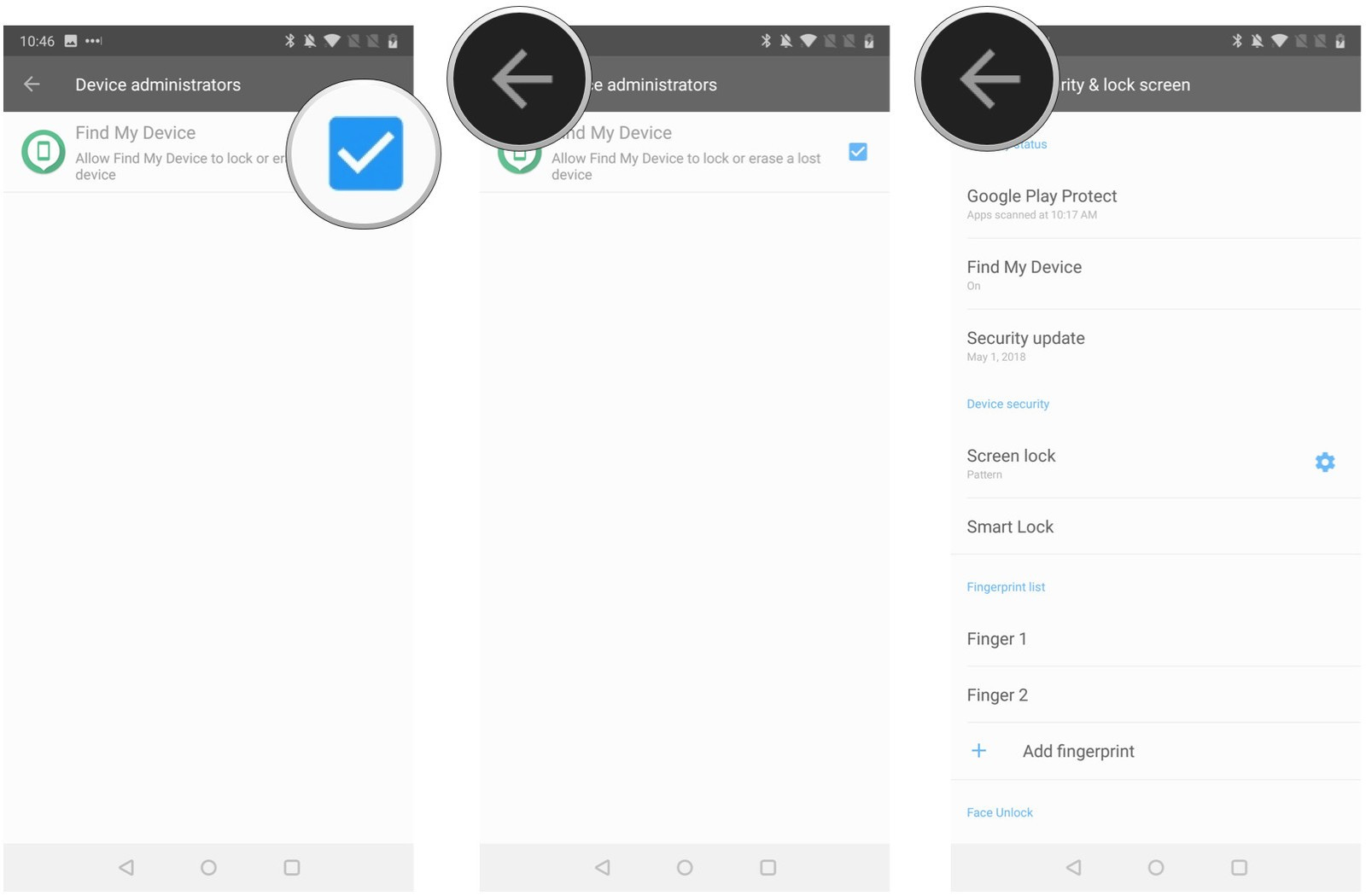
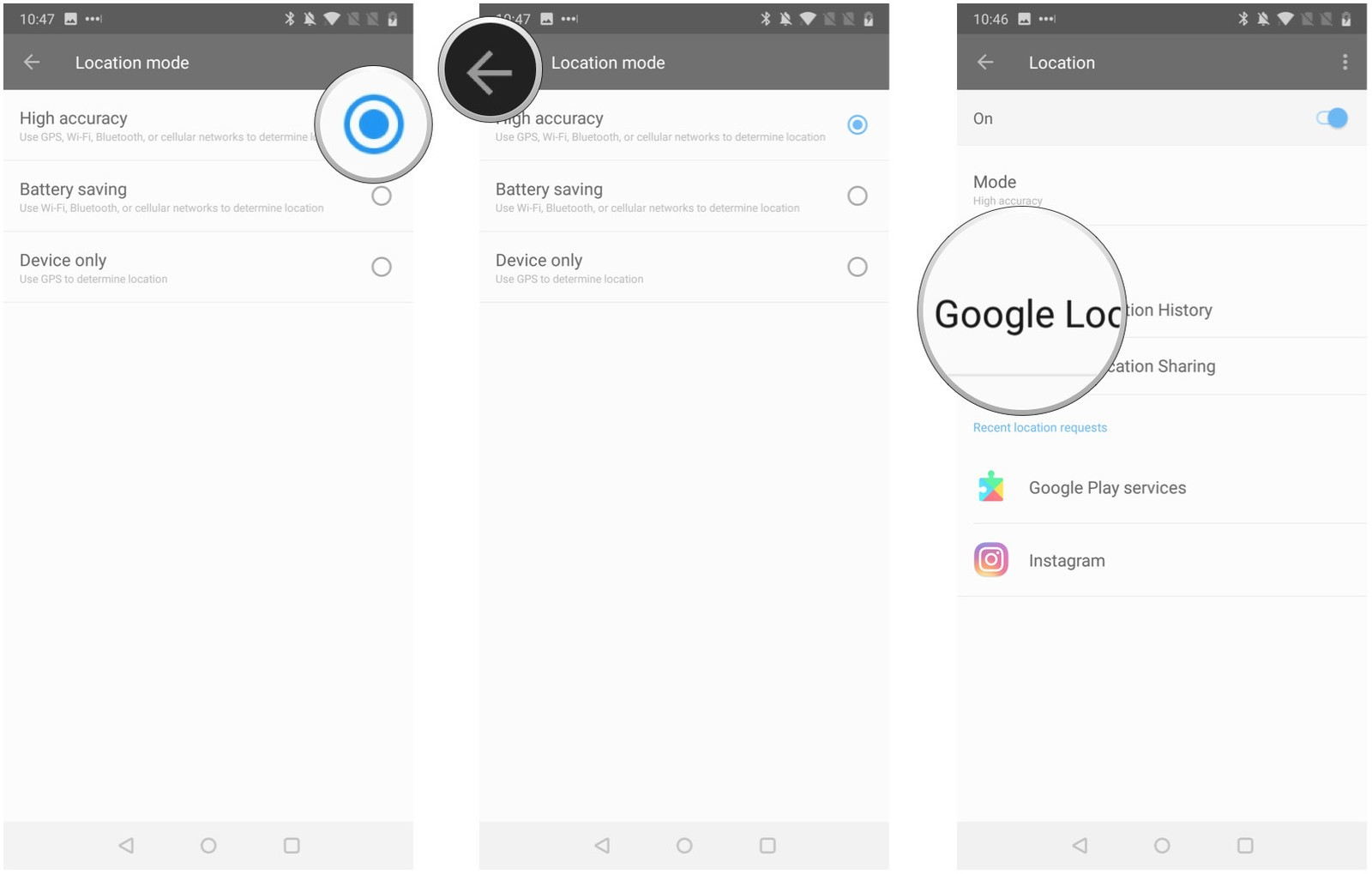
7. Click on Mod
8. Select High Accuracy to get a closer location
9. Again select back option on top left corner
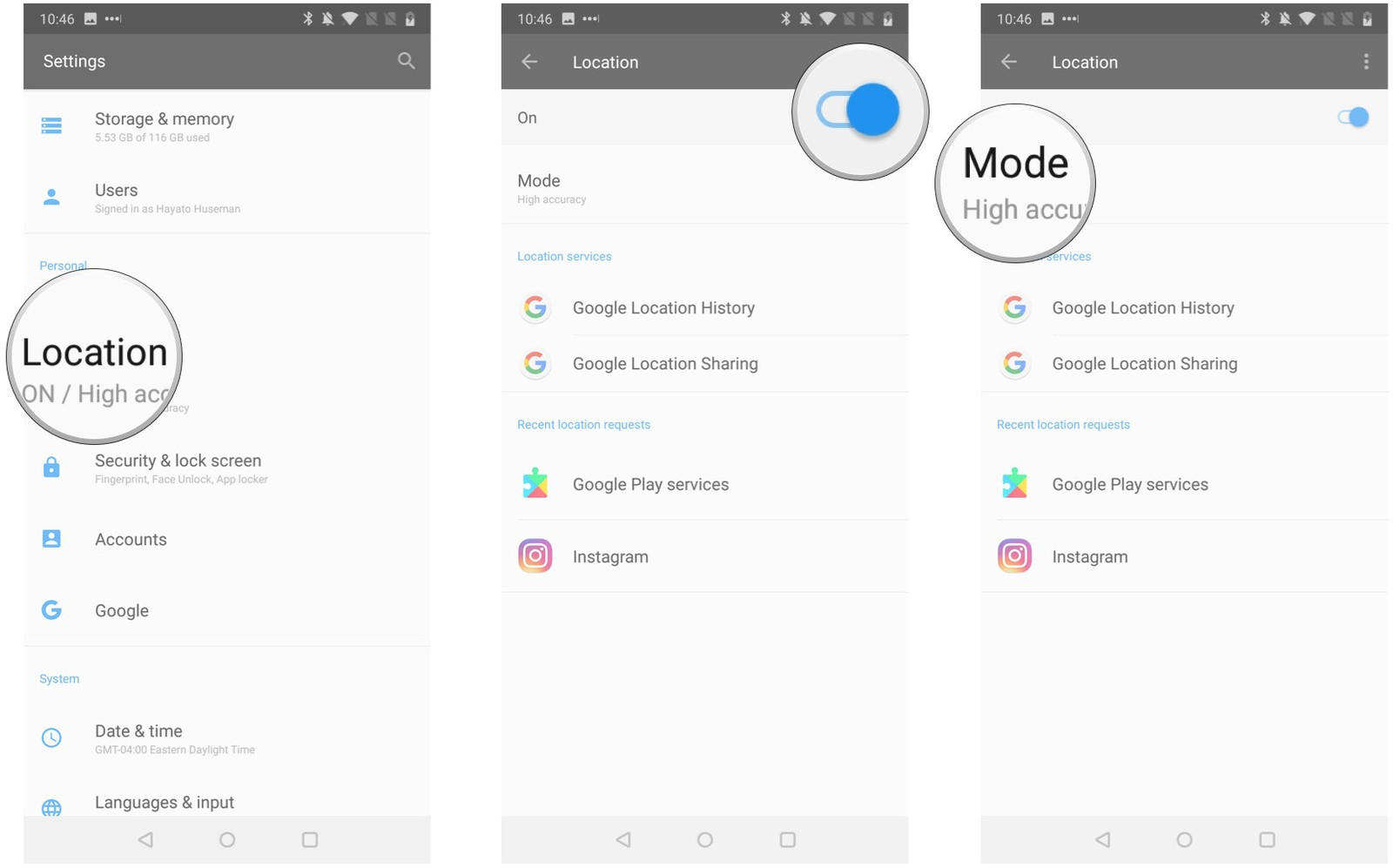
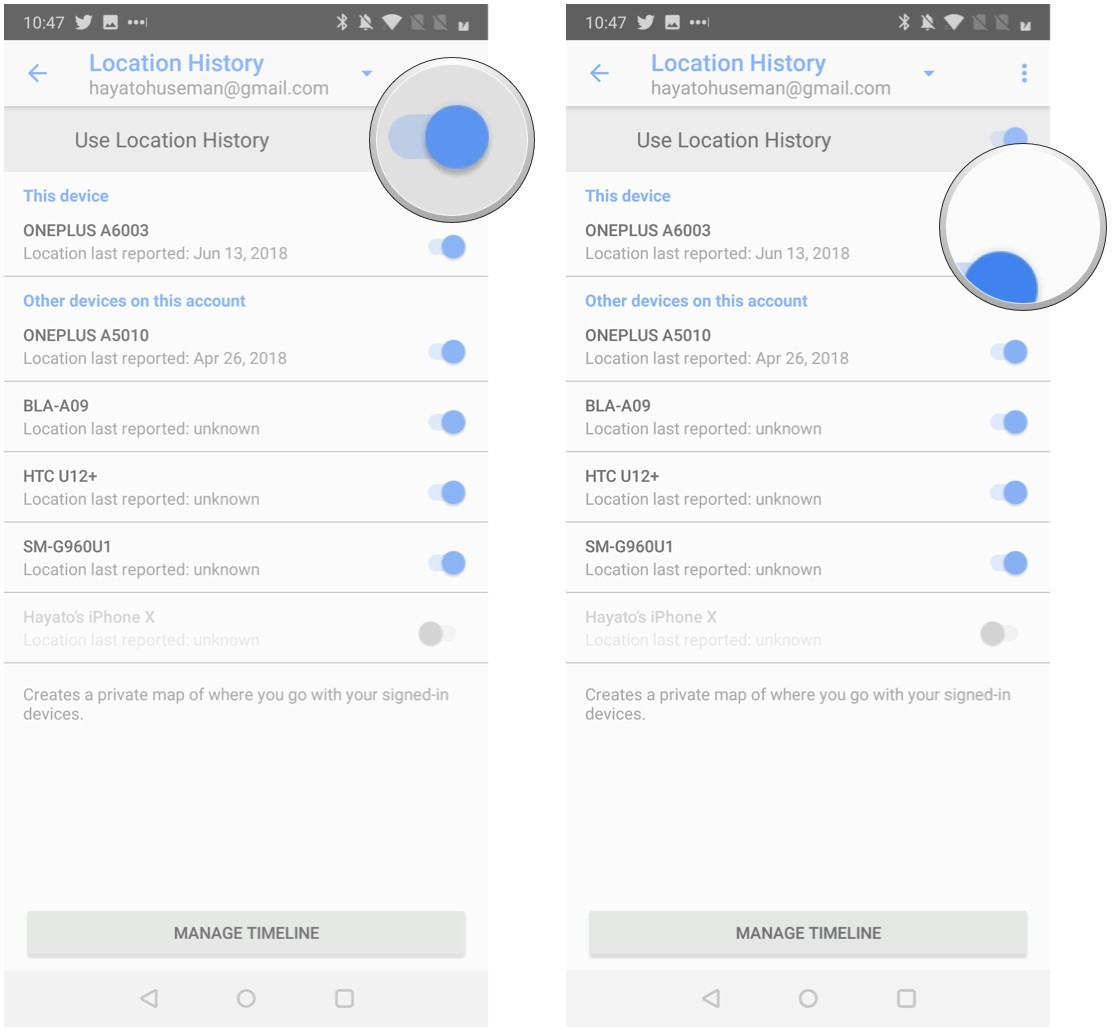
10. Tap Google location History
11. Switch on the Location History button
12. Switch on the button after your device name
13. You get your location on google map
2. Track with the help of Google
Google also helps in getting the location of your android phones. The process are as follows.
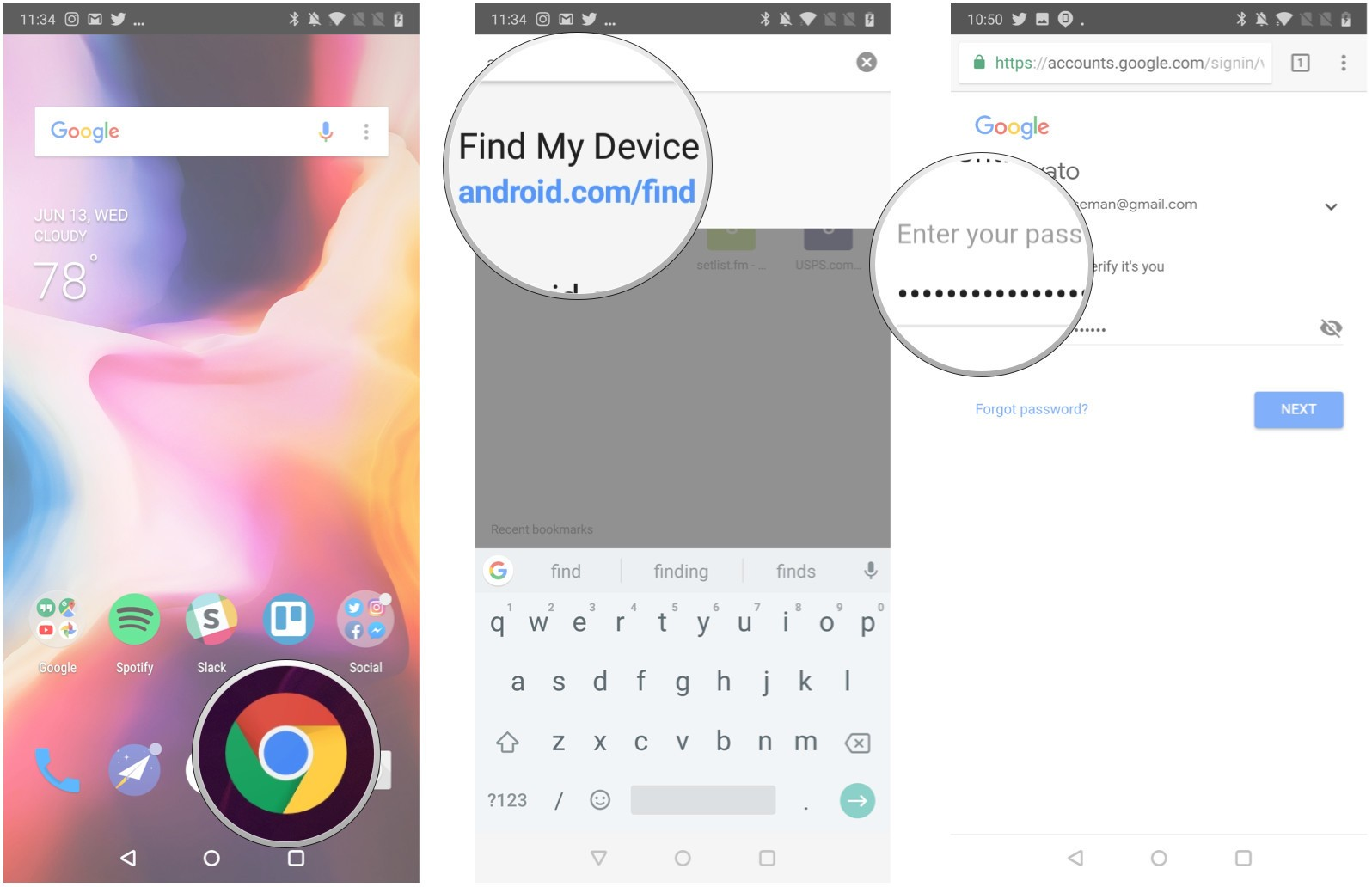
1. Open a web browser on your mobile, laptop or PC
2. Enter web address android.com/find
3. Enter your email address and password followed by a 2 step verification process after completing that process you will get the location on google map.
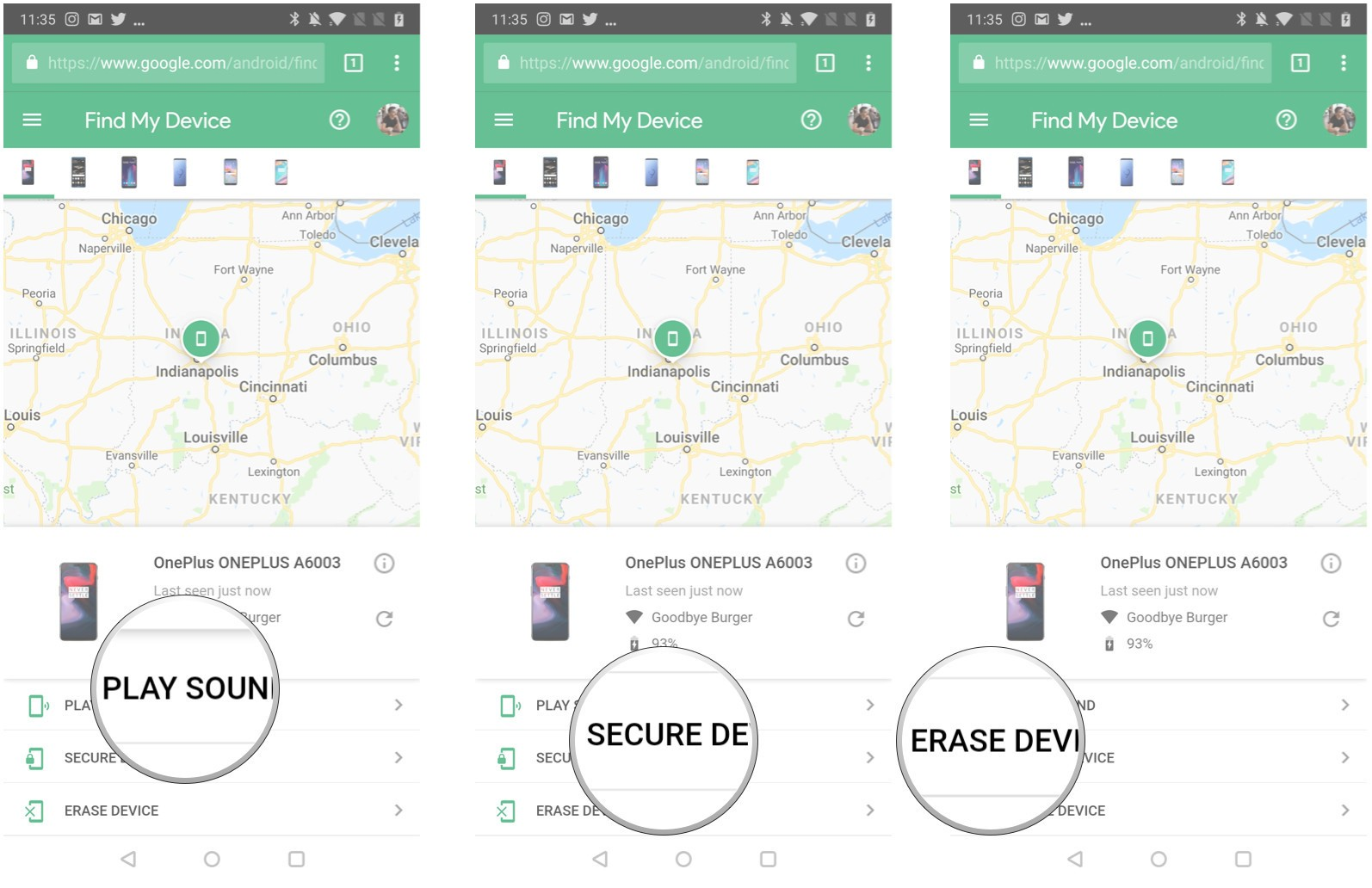
It also, enables you to perform these function.
● You can play sound So that your mobile can shout (high volume music) even if it silent.
● You can freeze your phone system so that no one can misuse your precious details like bank details, contacts, photographs etc.
● You can factory reset your phone so that all details are erased.
3. Track phone by the help of applications
While Google is an operating system provider. You can also track your phone by the help of third-party app several apps are available. We have made a list of some handpicked apps which you can try without any hassle.
1. Prey
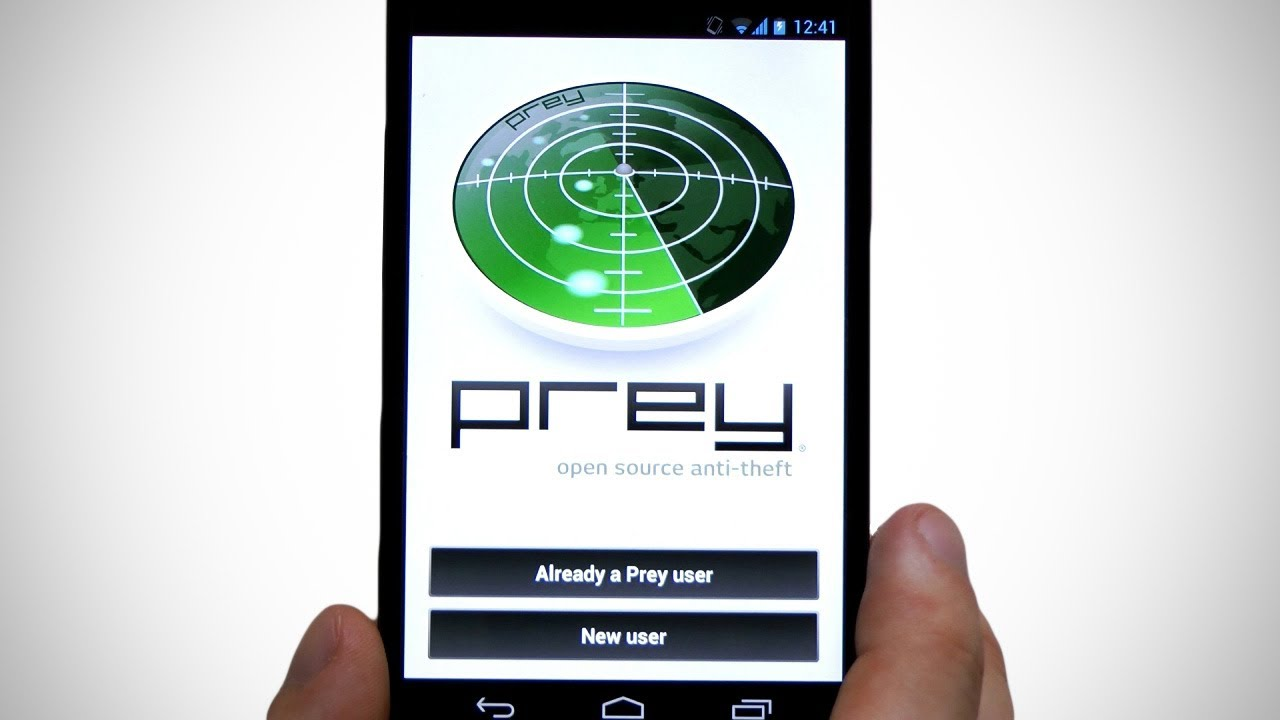
Prey is a great app as you lost or misplaced your phone just open your laptop and log into your account and start tracking.This App also gives feature of sending mails.you have to connect your gmail.com, www.Hotmail.com , or other Email Account to get updates by mails.
Prey runs smoothly in the background so you have not to worry about your privacy. It gives free use of up to 3 devices after they have paid plans.
2. Cerberus Anti Theft
Cerberus is one of the best anti-theft app available in the market. It empowers you to track or control your phone through website or SMS. You can switch on alarm, record audio or click pictures plus location history is the cherry on the cake. All this at a cost of $6 yearly only. Free trial for a week is also available.
3. Lookout
Lookout is an app which provides multiple benefits like tracking, antivirus, Malware protection etc.
It has an ability to record phones last location before the battery dies If someone tries to erase phone data or factory reset it automatically clicks the picture and email it to recovery email. They provide a two-week free trial. It is a paid app charge you $3 per month or $30 for a year along with many other premium services.
4. Accutracking
![]()
It a paid service which uses GPS to locate your phone. It works on most feature phone as well the only thing you need is your phone must be GPS enabled and it will provide your home location on GPS. It costs you $6 per month.
5. Avast Antivirus & Security

Avast is a big name in the world of antivirus and cybersecurity. It is a multiple app which facilitates you to scan virus, remove viruses, options for backup, power saving, anti-theft, Lock your smartphone, make your mobile to create noise consisting of a special feature name ‘Stealth’ so a thief will not be able to know that phone is protected by Avast Security. It is an All in One app providing premium services at its best.
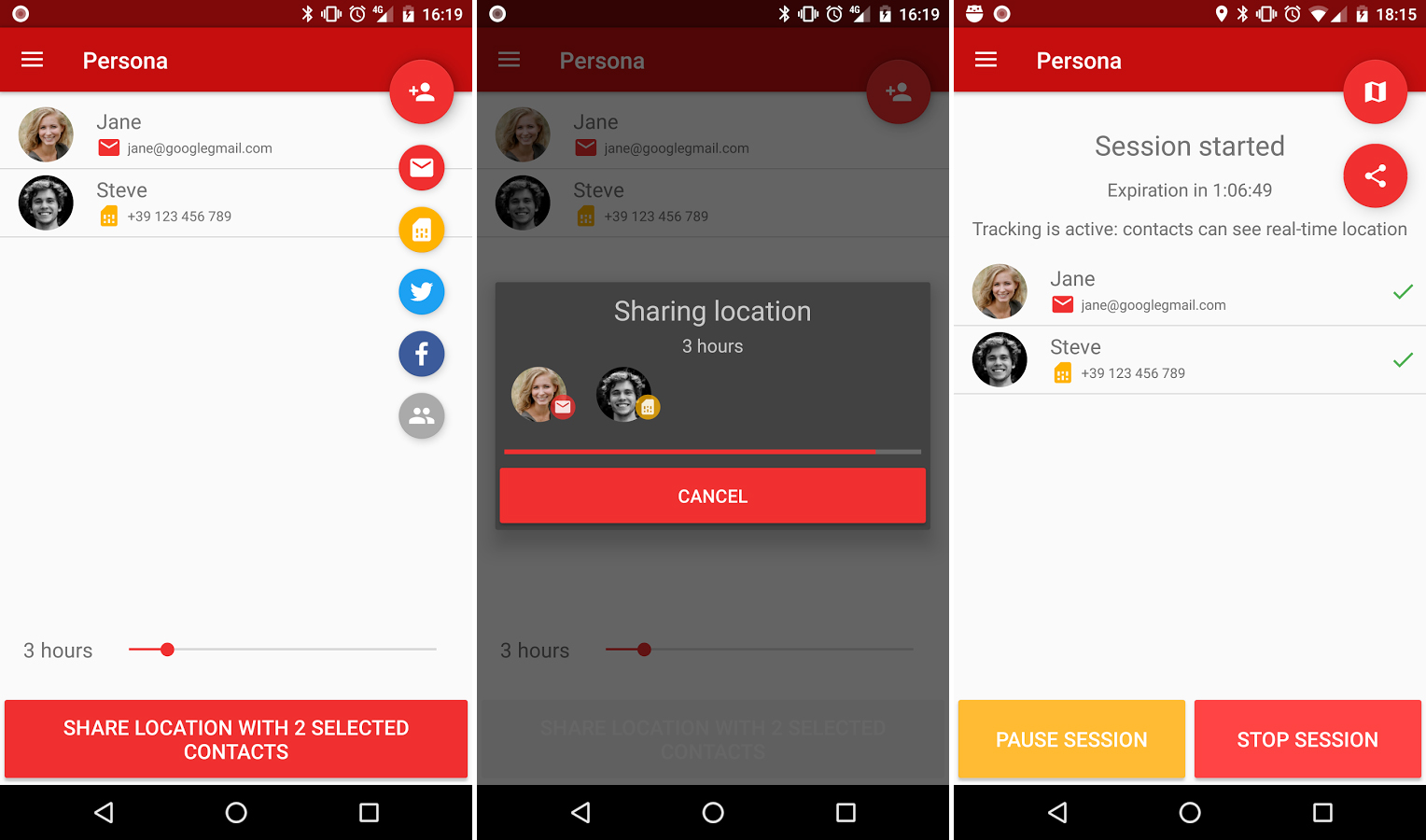
6. Family Locator

It is an advanced tracking mobile app by this you can track your phone as well as you can track your family member movement to ensure safety and security of your loved one. Even you can set alarms for your children in case they skip their daily routine like going to school or leaving school before time or bunking classes.
7. SeTracker
![]()
SeTracker provides you real-time locations with accurate details like longitude & latitudes also allows you to set geofences so that your phone will give a quick reminder to you and a heavy alarm through the speaker.
8. MMGuardian App
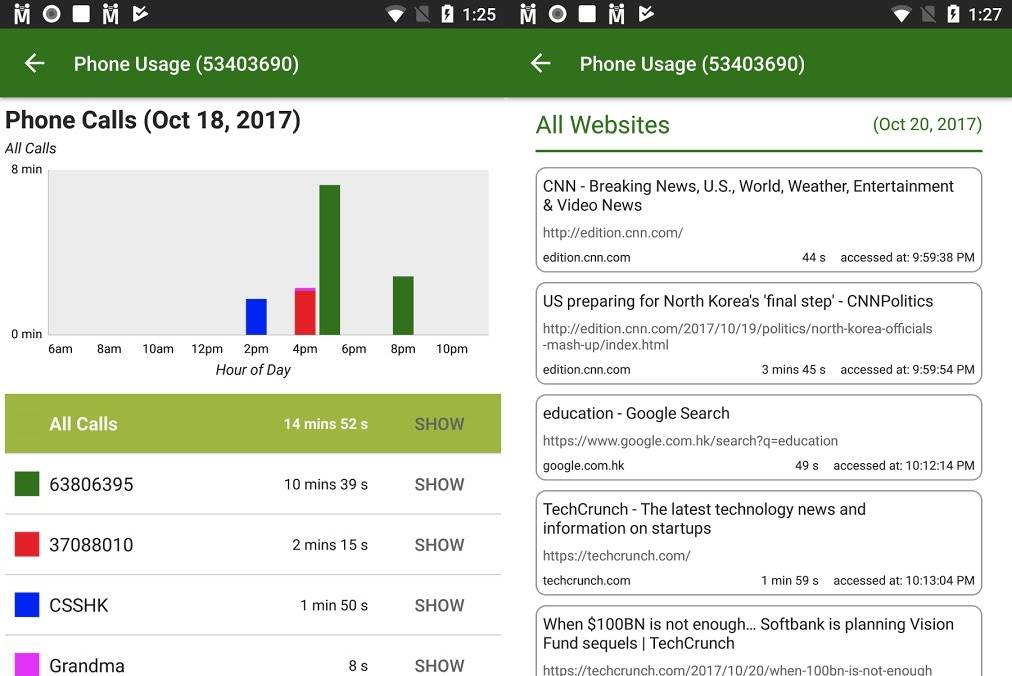
MMGuardian app is quick response tracking app through which you can easily track your mobile. In case of loss or theft inbuilt with a special feature. which allows parents to track the location of their kids to ensure security. Also can be very helpful in case of child kidnapping as it shows the location on a live map.You can block apps and websites as well by using this app.
So, these apps and services really help us to track our android devices. Some of them facilities us to track our loved ones in order to ensure their safety. Try these apps to explore their full functionality, If you know any app which you feels can have a place in this list share that in the comment box, any difficulty faced with mentioned apps and services comment will provide a solution and take care of that as well.
Helpful Resources:
1. 16 Best SEO Practices For Web Developers & Search Marketers
2. 16 Best (free) AMP – (Accelerated Mobile Pages) WordPress Plugins
3. Top 50 Best (Free) WordPress WooCommerce Plugins for your storefront
4. 16 Best Free SEO WordPress plugins for your Blogs & websites
-

 Instagram5 years ago
Instagram5 years agoBuy IG likes and buy organic Instagram followers: where to buy them and how?
-

 Instagram5 years ago
Instagram5 years ago100% Genuine Instagram Followers & Likes with Guaranteed Tool
-

 Business6 years ago
Business6 years ago7 Must Have Digital Marketing Tools For Your Small Businesses
-

 Instagram5 years ago
Instagram5 years agoInstagram Followers And Likes – Online Social Media Platform














