Electronics
How Smart Home Devices Can Streamline Your Daily Routine
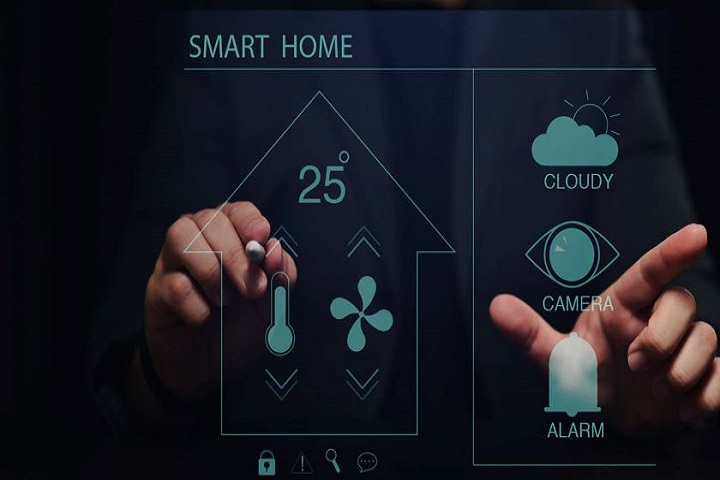
Smart home devices provide an opportunity for homeowners to have control over many aspects of their homes. How Smart Home Devices Can Streamline Your Daily Routine.
In today’s fast-paced world, where time holds immense value, there is a never-ending search to optimize our daily routines and enhance the efficiency of our lives. This is where smart home devices step in, showcasing remarkable technological advancements that can turn your living space into a hub of intelligence and seamlessness.
By 2027, it’s expected that this market will surge to $222.90 billion. From voice-controlled assistants to automated lighting and thermostats, these innovative devices provide a myriad of benefits that extend far beyond convenience, ushering in a new era of home technology.
Table of Contents
1. Next-Gen Technologies to Improve Daily Routines
By smoothly merging human pre-set commands with powerful technical systems, next-generation technologies have the potential to change our daily routines. These control centers for smart homes, known as smart hubs, represent the next wave of innovation that has the potential to totally revolutionize our lifestyles.
Users can gain a plethora of personal and environmental benefits by embracing this cutting-edge technology. Below, we look at some of the substantial benefits provided by these next-generation technological breakthroughs.
a. Enable Convenience & Comfort
Smart home devices provide an opportunity for homeowners to have control over many aspects of their homes. These gadgets enable the automation of everyday tasks like activating lights, regulating room temperatures, and securing doors. By seamlessly managing these functions, they enhance convenience, save valuable time, and simplify daily routines.
Smart tech gadgets empower users to automate everyday routines and create personalized schedules with more ease. No matter if it’s about illuminating your house and playing your jams upon arrival or adjusting the blinds depending on the time of day, these devices enrich your living experience by smoothly creating customized scenarios that correspond to your preferences.
b. Energy & money-efficient
Smart thermostats intelligently learn and remember your temperature preferences and thus optimize energy usage so you enjoy comfort while reducing wasteful consumption. Smart lighting systems can automatically detect room occupancy. Thanks to this feature, these systems know when to turn the lights off and thus minimize unnecessary electricity use.
As you can see, smart home devices enhance energy efficiency, which, in the long run, results in significant savings on utility bills. By remotely monitoring and controlling these devices, you can prevent energy waste by ensuring they are not inadvertently left on when not required.

c. Easy Access From Anywhere
Next-gen home devices grant you the ability to remotely control and monitor your home from anywhere, whether you’re at the office, enjoying a vacation, or connected to the Internet from any location. By utilizing an app on your smartphone or other devices, you can effortlessly manage and oversee various functions of your home, ensuring convenience and peace of mind even when you’re away.
d. Increased Safety & Security
With their focus on safety, these gadgets contribute to accident prevention and heightened security in your residence. For instance, intelligent smoke detectors can promptly send notifications to your mobile device in the event of a fire, enabling swift action. Similarly, smart door locks grant you the ability to verify and secure your doors remotely from any location, enhancing overall safety measures.
What’s more, there are gadgets specifically made as security systems. These provide comprehensive protection through advanced features like motion detection, surveillance cameras, and remote monitoring.
Real-time alerts and live feed access on your smartphone ensure constant vigilance, instilling peace of mind and deterring potential intruders. These robust security measures combine cutting-edge technology with convenience, safeguarding your home and loved ones.
e. Improve Accessibility
Smart home devices’ general advantages are very appreciated by individuals with disabilities or restricted mobility. Through voice-activated assistants and automated systems, these devices facilitate effortless control of various home functions, promoting inclusivity and independence for all, irrespective of physical capabilities.
2. Smart Devices & Their Environmental Impact
As previously stated, smart home devices have many benefits, but one of the most important is that they encourage environmental sustainability by prioritizing energy efficiency. Specifically, whether you use a smart light bulb or connect your TV to your assistant, all smart home devices considerably reduce carbon emissions and the overall environmental footprint. Users who use these technologies can actively contribute to resource conservation and a greener, more sustainable future.
3. Final Thoughts: Are Smart Home Devices Needed?
Smart home technologies provide many advantages that can help streamline and improve our daily lives. These revolutionary technologies are changing our living environments into intelligent and seamless hubs of convenience, with the market anticipated to reach $222.90 billion by 2027. These technologies save time, simplify our lives, and provide unprecedented comfort and control by automating tasks, enabling customizable scheduling, and providing simple access from anywhere.
Furthermore, they encourage energy and cost efficiency, strengthen safety and security, and improve accessibility for people with impairments. Importantly, smart home gadgets promote environmental sustainability by lowering carbon emissions and encouraging resource conservation. As we adopt next-generation technologies, we pave the path for a greener, more sustainable future for our homes and communities.
About the Author:
David Todva is a renowned freelance writer for The Next Tech based in the US. He has been in the industry for many years and has earned a reputation as an accomplished writer, specializing in technology innovation with a focus on home security.
-

 Instagram5 years ago
Instagram5 years agoBuy IG likes and buy organic Instagram followers: where to buy them and how?
-

 Instagram5 years ago
Instagram5 years ago100% Genuine Instagram Followers & Likes with Guaranteed Tool
-

 Business6 years ago
Business6 years ago7 Must Have Digital Marketing Tools For Your Small Businesses
-

 Instagram5 years ago
Instagram5 years agoInstagram Followers And Likes – Online Social Media Platform














