Technology
The Salient Features of MongoDB That Makes It So Popular in 2019
MongoDB Database is a document-oriented database & NoSQL database. The Salient Features of MongoDB Database That Makes It So Popular in 2019.

The phenomenon of increasing data all over the world has been of significant interest and so organizations and businesses are looking for novel and more efficient techniques of managing the gigantic flood of data. They are more and more attracted by the alternate database management applications and tools as opposed to the traditional or the conventional relational database systems. MongoDB is one such cutting-edge and useful unconventional database management system.
Table of Contents
What is MongoDB?
According to https://intellipaat.com, Mongo DB could be defined as an effective open-source database which utilizes a document-based data model along with a popular non-structured query language. MongoDB is supposed to be a powerful and competent NoSQL system that is stealing the show today in the global database software market. Here are some of the striking features of Mongo DB.
Ad-Hoc Queries
Usually, while designing a database’s schema, you would not know in advance the queries that would be performed. You must know in this context, ad-hoc queries are queries that are unknown at the time of structuring the database. Hence, we find that MongoDB is effective in providing solid ad-hoc queries support that makes it really more special. Ad-hoc queries actually seem to be updated very much in real time, culminating in enhancements and boosts in performance.
Schema-Less Database
In the case of Mongo DB, we understand that one collection would be holding different documents. MongoDB has absolutely no schema hence; it could be having numerous fields, size, and content differing from another document belonging to the same collection. MongoDB is known to demonstrate flexibility while dealing with and effectively handing the databases. You may seek the expert services of RemoteDBA.com for the perfect solution.
Document-Based
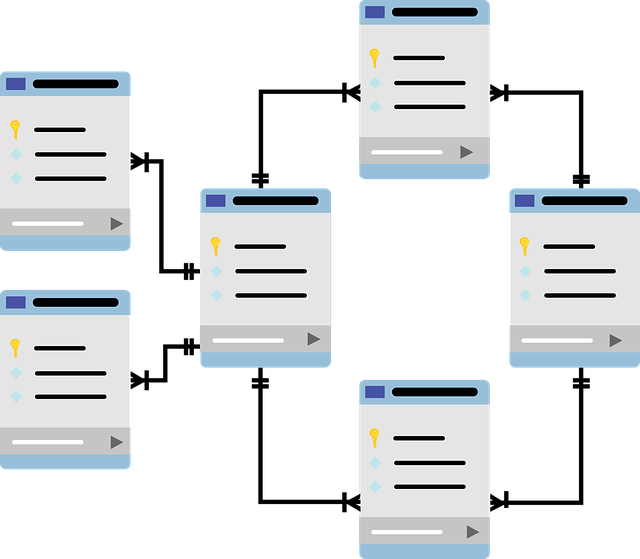
MongoDB is actually a document-based database that is an amazing characteristic in itself. We know that in the case of the relational databases, you would be finding rows and tables for data arrangement. Each and every row would be having a specific number of columns. These columns are known for storing a precise kind of data. However, in the case of NoSQL the rows and tables are substituted with fields. There seem to be different documents that could be storing diverse types of data. We understand that there are collections or groups of similar documents. Every document is supposed to be having a key ID that is unique or even a unique object ID that could both be user or system-defined.
Indexing Out of the Box
Indexes are used to optimize search performance. MongoDB allows any field in a standard document to be indexed using primary and secondary indexes. This ability to resolve queries rapidly and efficiently is among the best features of the platform and has earned it a lot of praise from the developer community. MongoDB’s database engine uses a predefined index which maps fields and can be used to find documents that are compatible with a particular query, thus vastly improving performance. This becomes even more evident if a document is queried repeatedly- you will certainly appreciate the speed boost.
Replication and Redundancy
MongoDB uses replication to achieve redundancy. This essentially means that the data for the application is distributed across multiple machines. Essentially, there will be a set of primary nodes, and one or multiple sets of replica nodes. Replication is extremely important for contingency management. Replica sets follow the principle of master-slave replication, which means there is a master node, which can perform read and write activities, while the slave nodes can only copy the data from a corresponding master node (read-only) without changing its values.
MongoDB replica sets also feature something called the automatic failover. In case the primary node is down for over 10 seconds or fails an integrity check, the system can consider a secondary instance to be the new primary. This allows uninterrupted, smooth operation and also saves a considerable amount of time that would have gone into maintenance and data recovery. When the previous primary node is back online, it will enter the pool as a second instance to be elected in the future by the replica set. This high-availability low-downtime model is the key to production-ready systems that MongoDB is deployed in.
Aggregation
MongoDB is supposed to have an integration framework that is great for efficient usability. You could be successfully batching process data and getting a single outcome even after performing diverse operations on the group or collection data. We know that the map-reduce function, single-purpose aggregation, and the aggregation pipeline methods are supposed to be three effective ways of providing an aggregation framework.
GridFS
A striking feature of both storing and even retrieving files is called GridFS. For files over 16 MB, this specific feature is supposed to be quite useful. GridFS would be effectively dividing a particular document into parts referred to as chunks and storing them properly in another separate document. The default size of all these chunks barring the last chunk would be 255 KB.
Sharding
While dealing with bigger datasets, sharding as a concept is introduced. This humungous data could result in some issues in case a query comes regarding them. Sharding is a striking feature that would be assisting in the distribution of this problematic data among multiple MongoDB instances. The collections found in MongoDB that has a relatively bigger size are actually distributed in several collections. All these collections are referred to as shards and they are actually implemented by clusters.
High Performance
MongoDB is supposed to be a competent open source database that offers high performance. This demonstrates scalability and high availability. It would be having really faster query response simply because of replication and indexing. This would be the reason why MongoDB must be regarded as the right choice for real-time and big data applications.
MongoDB Management Service
MMS is a robust web tool for effective database tracking and even for backing up your data. We are told that MMS is also tracking hardware metrics to effectively manage a MongoDB deployment. It would be demonstrating performance in a fully-featured web console for assisting you in optimizing your deployment. It would also, be providing characteristics such as custom alerts that should help you in discovering issues much before your MongoDB instance would be impacted.
Conclusion
We have mentioned some of the important features and characteristics of MongoDB such as Sharding, High Performance, Aggregation, Ad-Hoc Queries, Indexing, Replication, and Schema-Less database, GridFS, etc. You must know the advantages and disadvantages associated with MongoDB.
Helpful Resources:
1. 16 Best (free) AMP – (Accelerated Mobile Pages) WordPress Plugins in [2019]
2. 16 Best Free SEO WordPress plugins for your Blogs & websites in [2019]
3. Riverdale Cast List For The TV Show Riverdale
4. Top 25 Best SolarMovie Alternatives in [2019]
5. How to Protect WebSites Against Attackers or Hackers by using “X-Security Headers”.
-

 Instagram5 years ago
Instagram5 years agoBuy IG likes and buy organic Instagram followers: where to buy them and how?
-

 Instagram5 years ago
Instagram5 years ago100% Genuine Instagram Followers & Likes with Guaranteed Tool
-

 Business6 years ago
Business6 years ago7 Must Have Digital Marketing Tools For Your Small Businesses
-

 Instagram5 years ago
Instagram5 years agoInstagram Followers And Likes – Online Social Media Platform














