Computer
Reload Button – Hard Refresh Chrome | Refresh Computers (F5) | Different Ways to Reload Web Pages Using Function Keys?
Reload Button is also known as refresh & reload a browser feature that provides users with the latest version of the web pages. Hard Refresh Chrome & Refresh Computers (F5).

Reload Button is also known as refresh and reload a web browser feature that provides users with the latest version of the web pages. See our browser definition for further information about the reload button, as well as follows.
On any web browser, you can press the F5 function short key to reload a web page. On the off chance that you don’t have an F5 key, you may likewise press the CTRL+R alternate quick keys.
You are pushing CTRL+F5 hard to the full refresh of the web page, causing the web browser not to reload any page content from an update. Doing so can help guarantee all the content on the website page is the latest, and new content will be displayed.
Browser cache is helpful for fast web browsing, yet a specific pain point for web developers. Refresh Computers (F5) and Hard Refresh Chrome
Advanced modern-day browsers these days cache each front end asset like javascript or CSS. They principally do this to improve the site performance.
In any case, this can be genuinely bothering while one is being developed mode and continually adjusting the javascript or CSS. The best way to see the changes is by doing a hard refresh chrome or clear the cache of the web browser.
A hard refresh chrome is a method for clearing the chrome browser cache for a particular page to force it to reload button, the latest version of a web page is loaded.
Once in a while, when changes are made to the website, they don’t enroll quickly due to browser caching. A hard refresh chrome will, for the most part, fix this, however at times, totally clearing the browser cache is essential.
Table of Contents
1. Different Ways to Reload Web Pages Reload Button Using Function Keys
There are Normal Reload or soft Reload. Check it out the short keys below to reload button.
- F5 – Normal Reload or soft Reload
- CTRL+F5 – Hard Reload button
- CTRL+R – Normal Reload or soft Reload
- CTRL+SHIFT+R – Hard Reload
- CTRL+WINDOWS+F5 – Hard Reload
2. Reload Button to Resubmit
Reload button to resubmit the latest content of the web pages on web browsers. When we hard reload and soft or normal reload, browsers will fetch the resubmit current page data on web browsers to avoid the browser cache.
3. Reload Button – Hard Refresh Chrome (CTRL+F5) – Refresh Computers (F5)
Press reload to resubmit the data latest web page content when we reload the refresh button or function keys. Web browsers will skip the web browser cache and showing the latest or fresh pages on the browser.
4. How to do Hard Refresh on Different Web Browsers?
Hard Refresh in Chrome, Firefox, Safari, and IE or Edge Browser

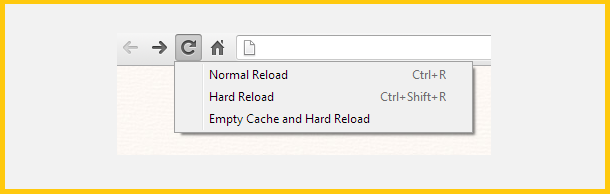
5. Hard Refresh Chrome
Hard Refresh Chrome is a quick way to reload button means hard refresh should be possible by following shortcuts. Refresh computers systems by using the function key-F5
6. Windows/Linux (Refresh Computers-F5)
Hold down CTRL & Click the Reload.
Or then again, Hold down CTRL and Press F5.
Open the Google Chrome Dev Tools by pressing F12. When the chrome dev tools are open, correctly click on the reload button, and a menu will dropdown. This menu gives you the choice of doing a hard refresh chrome, or in any event, clearing the cache and do a hard refresh automatically.
7. Mac or Macintosh (Refresh Computers-F5)
Hold ⇧ Shift and click the Reload button.
Or then again, hold down ⌘ CMD and ⇧ Shift key and afterward press R.
Mozilla Firefox & Related Browsers:
8. Windows/Linux
Hold the CTRL short key and press the F5 key.
Or on the other hand, hold down CTRL and ⇧ Shift and afterward press R.
9. Macintosh or Mac
Hold down the ⇧ Shift and click the Reload button.
Or on the other hand, hold down ⌘ CMD and ⇧ Shift and afterward press R.
10. Internet Explorer (IE) or Edge Browser
Hold the CTRL key and press the F5 key.
Or then again, hold the CTRL key and click the Refresh button.
-

 Instagram5 years ago
Instagram5 years agoBuy IG likes and buy organic Instagram followers: where to buy them and how?
-

 Instagram5 years ago
Instagram5 years ago100% Genuine Instagram Followers & Likes with Guaranteed Tool
-

 Business6 years ago
Business6 years ago7 Must Have Digital Marketing Tools For Your Small Businesses
-

 Instagram5 years ago
Instagram5 years agoInstagram Followers And Likes – Online Social Media Platform














