Gadgets
Problem Solved – MacBook/Mac is Not Recognizing External Hard Drive.
Problem Solved – MacBook/Mac is Not Recognizing External Hard Drive. Use a different USB port/adapter/cable. Reboot the MacBook

After you connect a removable disk through the computer’s USB port or SD card slot, the Mac OS will read the drive and mount it on the desktop, in Finder, and Disk Utility. The Mac OS always enables you to have the most convenient access to open the disk and manage files on it.
However, people may not go as quickly as you expect. MacBook Air/Pro may not show up the external hard disk at all. One the one hand, the disappeared disk icon makes it inconvenient to open the drive. On the other hand, the disk might be corrupted and result in data loss or difficulties in file transfer.
After reading the article, you will learn:
- Why the MacBook doesn’t recognize the external hard drive
- How to make the MacBook detect the external hard drive
- Solving external hard drive not showing up problem
- An easy way to recover data from the unrecognized external hard drive
Table of Contents
1. Why is the MacBook not recognizing my external hard drive?
The recognition process of an external device contains two parts – hardware and software. Any problems in either of the two parts will end up with the macOS doesn’t detect and recognize the external hard drive.
We summarize four common reasons:
- The USB port/USB adapter/USB cable is broken.
- The external hard drive is physically damaged.
- The incompatibility between the file system of the external hard drive and the Mac OS.
- The file system/partition table/other core information on the external hard drive is corrupted.
2. How to make the MacBook detect my external hard drive?
The very first step of solving the problem is to check the hardware conditions of the connection and the hard disk itself.
a) Use a different USB port/adapter/cable
After plugging and unplugging for multiple times, the USB/port/adapter/cable may get worn out or become wobbly if you have spare ones, the go-ahead to use them.
b) Reboot the MacBook | MacBook Not Recognizing External Hard Drive
If you didn’t eject an external drive safely before you attach another one to the MacBook laptop, the computer might believe the USB port is still unavailable. As a result, the MacBook may not accept another external drive. Then you need to restart the computer and reconnect the external hard drive to it. After rebooting, the OS will release the USB port to the external hard drive.
c) Connect the external hard drive to another computer
If you are sure that the USB port/adapter/cable is all good and you have restarted the MacBook, but the problem stays unsolved, try to find another Mac or PC to see if the external HDD can be detected. Did you ever drop the external hard drive? If you did, the disk might suffer physical damages that prevent it from working correctly. Let it go and get a replacement.
3. Solving the external hard drive not showing up problem
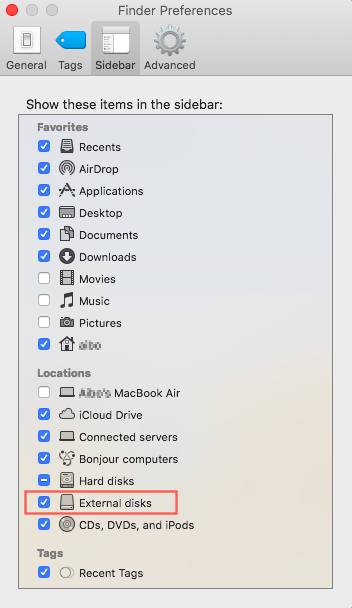
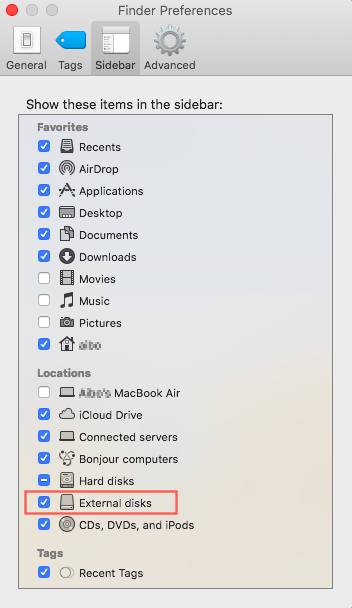
Sometimes, your external hard drive is recognized by macOS, but it doesn’t show up on the desktop or in Finder. It makes you feel your external HDD is not known. To see if that is the case you come across, go to verify a few settings.
Go to the top menu bar where the Apple logo is and click on “Finder.” Select “Preferences,” and you will see four tabs on the top. Tick “External disks” under “General” and “Sidebar” tabs. Then the MacBook is set up to show up the external hard drive on the desktop and in the Finder.
If all settings look useful to you, the removable hard disk not showing up problem might result from the incompatibility between the file system and the MacBook, or the corrupted file system of the external hard drive. To make the external HDD work properly on MacBook, you need to erase it in Disk Utility. A small reminder: the erasing will deleted all your data.
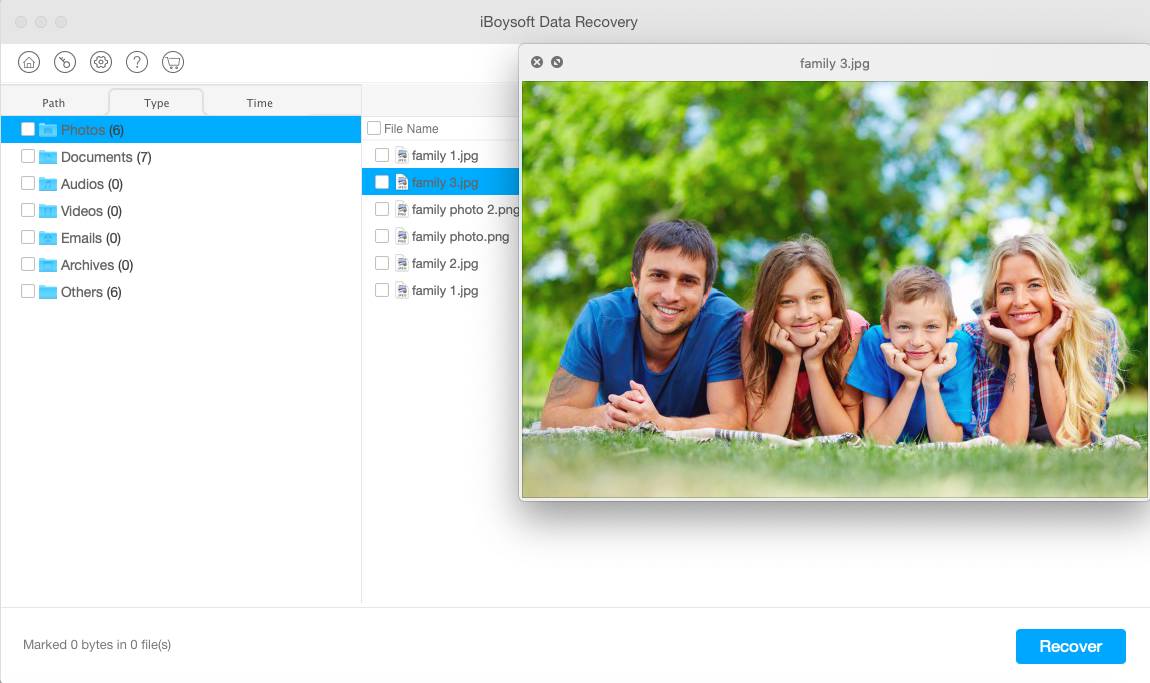
4. An easy way to recover data from the unrecognized external hard drive
Many people probably won’t realize that they are facing a threat of data loss until they are. Fortunately, professional and reliable ransomware data recovery services are available for you. They are very efficient in restoring the essential pictures, videos, documents, and other files from the unrecognized external hard drive.
5. A final note
When the external hard drive suddenly becomes unrecognizable on Mac, don’t be panic because you can fix the problem by merely correcting the hardware connections or reformatting the disk. You may find more information about the unrecognized external hard drive on Mac in this post.
-

 Instagram5 years ago
Instagram5 years agoBuy IG likes and buy organic Instagram followers: where to buy them and how?
-

 Instagram5 years ago
Instagram5 years ago100% Genuine Instagram Followers & Likes with Guaranteed Tool
-

 Business6 years ago
Business6 years ago7 Must Have Digital Marketing Tools For Your Small Businesses
-

 Instagram5 years ago
Instagram5 years agoInstagram Followers And Likes – Online Social Media Platform