Computer
How to Recover Lost Data on Mac Using Wondershare Recoverit
Mentioning the market leaders, Wondershare Recoverit is trusted by millions of users globally and can save data from all kinds of disasters.

The expansive data management needs of today often pose the inconvenience of information mishandling and unwanted loss. As a result, there is a constant need for data recovery solutions to avoid data loss situations. Likewise, there is a diversity of free data recovery software for getting back lost data.
Mentioning the market leaders, Wondershare Recoverit is trusted by millions of users globally and can save data from all kinds of disasters. We will mainly talk about its Mac-compatible utility for retrieving lost data in enough detail.
Table of Contents
Part 1: Recoverit Mac Data Recovery Overview
Available for Windows and Mac devices, Recoverit is excellent for getting back your lost data files quickly and conveniently. This data recovery software is packed with a vast variety of new and exciting features that promise a high-speed and accurate recovery of your lost data in more than 1000 file formats, such as audio, video, photo, Office documents, email, etc.
Recoverit is efficient enough in getting back the lost data in more than 500 different scenarios, from over 2000 devices. You can safely retrieve deleted, lost, and formatted information from USB flash drives, SD cards, internal and external hard disks, cameras, memory cards, etc.
More importantly, it retains the original quality and resolution of the recovered data for the user’s convenience. You can hence, rest assured of the file settings of your high-resolution images, videos, and audio files.

Part 2: How to Recover Lost Data on Mac with Recoverit Mac Data Recovery?
Situation 1: Recover Data from Bootable M1/T2 Mac Hard Drive/Trash/HDD
Visit the official website to download and install Recoverit Mac Data Recovery on your Mac device. Launch the tool and take the following steps:
Step 1: Choose a Location
In the program’s welcome interface, head to the left side panel and select the desired location for retrieving lost data. Tap the ‘Start’ button to proceed further.
Step 2: Location Scanning
As you click on ‘Start’, the software initiates an automatic scanning of the selected location for recovering the lost files. To recover videos, you can try the ‘Advanced Video Recovery’ feature for retrieving large-sized video files without corruption.
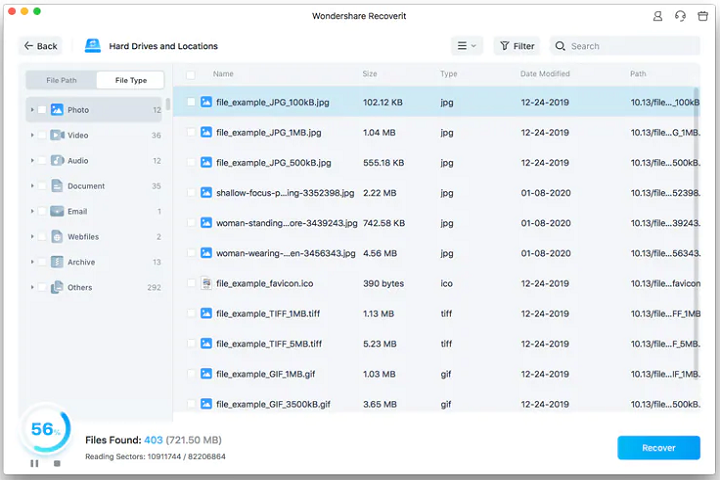
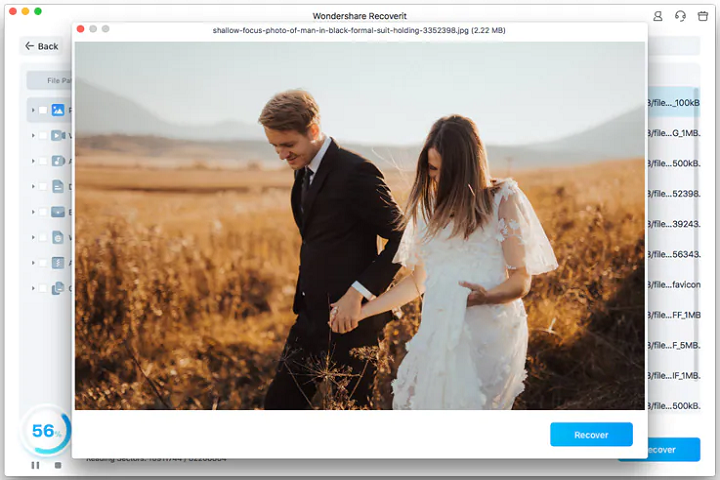
Step 3: Let’s Preview and Recover!
As the scanning progresses, the lost files appear sequentially on the screen. You can select the required ones to preview each and tap the ‘Recover’ button to retrieve them.
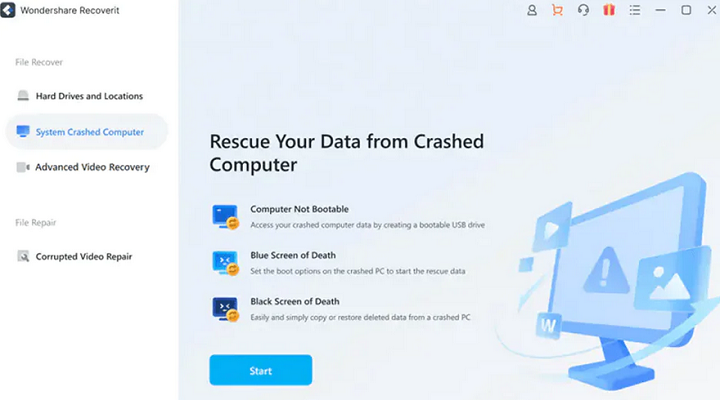
Situation 2: Recover Data from Unbootable Mac M1/T2 with Wondershare Recoverit
Recovering data from an unbootable M1/T2 Mac drive requires you to create a bootable drive. The process is easy with Recoverit.
Requirements for Creating a Bootable Drive
- A normally working system
- A USB flash drive
- The Thunderbolt 3 (USB-C) or Thunderbolt 3 USB cable will be connected to the new computer, as the alternate bootable media.
Download, install and launch Recoverit Mac data recovery and take the following steps:
Step 1:
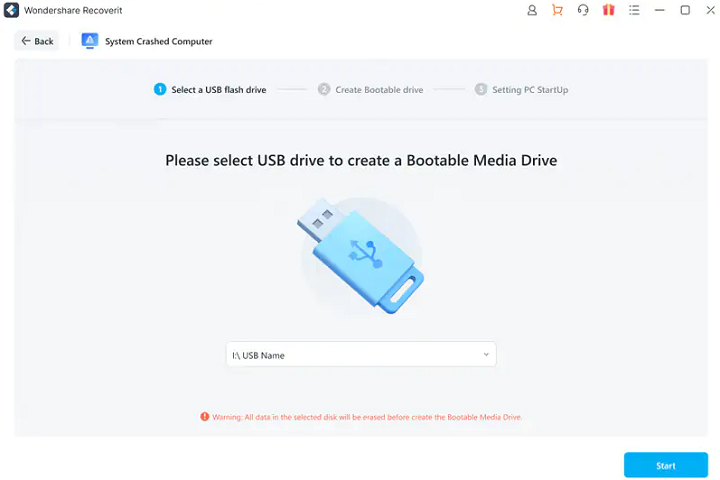
Click on the ‘System Crashed Computer’ option on the main page. Insert the blank USB in the system’s USB port and hit ‘Start’.
Click on the USB name and tap ‘Start’ again. A warning message appears on the screen. Select the ‘Format’ option from here and it will show you the procedure for formatting the USB drive.
Step 2: Creating the bootable media
After the formatting, the bootable media drive will be created on Mac. During the process, do not remove the USB flash drive from your Mac computer
Step 3: Finish creating bootable media
Then Recoverit will guide you to boot your crashed Mac from a USB flash drive
Step 4: Recover data from crashed Mac
Select the file copies, followed by connecting an external drive to your unbootable Mac. Choose the hard drive as the new storage location. Click on ‘Start Copy’ for moving the files to the connected USB.
Part 3: Main features of Recoverit Mac Data Recovery
Recoverit Mac Data Recovery welcomes users with a host of appealing features and functionalities. No wonder the software tops user preferences among the diversity of data recovery solutions available. The following section outlines some of the promising features of this program:
- Fully compatible with Apple T2 security chip-enabled Macs.
- It is an excellent solution to recover lost data files of almost any format. You can get back all your important audio, documents, emails, and favorite images, videos, and graphics.
- Allows you to get back lost data due to accidental deletion, disk formatting, device corruption, system crashes, bootable issues, virus attack, emptied recycle bins, partition loss, etc.
- Offers an exclusive file preview feature that allows you to check the files before recovering them.
- Super easy to use, even if you don’t have any tech background. Also, the development team extends 24 x7 tech support for the user’s convenience.
Part 4: Price and Plans
The software is available for free trial and subscriptions at convenient prices. You can recover up to 100 MB of data for free.
- Essential Plan: $79.99/ Year, supports unlimited data recovery for 1 Mac.
- Standard Plan: $99.99/ Year, support computer crash recovery plus unlimited data recovery for 1 Mac.
- Premium Plan: $139.99/ Year, supports advanced video recovery & repair, plus computer crash recovery, and unlimited data recovery for 2 Macs.
Conclusion
Data recovery programs are the need of the hour, in light of modern-day information handling requirements. Looking into the software diversity, you can choose from an extensive range of tools. When aiming to recover lost data on a Mac device, the Wondershare Recoverit Mac Data Recovery software can be preferred without a second thought.
The tool has a host of features to facilitate quick and efficient retrieval of lost data on Mac utilities. The scenario and format support of the tool is endless, and the preview capability is an added advantage. The software can recover data from bootable the Apple M1 chip.
-

 Instagram5 years ago
Instagram5 years agoBuy IG likes and buy organic Instagram followers: where to buy them and how?
-

 Instagram5 years ago
Instagram5 years ago100% Genuine Instagram Followers & Likes with Guaranteed Tool
-

 Business6 years ago
Business6 years ago7 Must Have Digital Marketing Tools For Your Small Businesses
-

 Instagram5 years ago
Instagram5 years agoInstagram Followers And Likes – Online Social Media Platform














