Cybersecurity
Time is now: vacancies for more cybersecurity experts increasing
Cybersecurity experts have an important role in this, as well as all users. Let’s look further into it. Importance of protecting online data.

The advance of technology continues, and every day, the digital world becomes more part of our daily lives. We use the internet to communicate, work, shop, and entertain ourselves. However, this increased reliance on technology also means that our online data is more vulnerable than ever before. Cybercriminals are constantly looking for ways to break into our personal information, and the consequences can be devastating.
This opens opportunities for exciting careers that are going to help create a digital world where it is safe to navigate and maintain a lifestyle that is pleasant and practical. Cybersecurity experts have an important role in this, as do all users. Let’s look further into it.
Table of Contents
1. The importance of protecting online data
Protecting your online data is crucial to safeguarding your identity and preventing cybercriminals from accessing your personal information. Your online data includes your email, social media accounts, banking information, and any other sensitive information that you share online. If such data falls into the hands of malicious entities, it could be exploited to steal your identity, perpetrate financial fraud, or even blackmail you.
In addition to protecting your personal information, safeguarding your online data is also essential for protecting your online reputation. Online attacks can damage your reputation by spreading false information or inappropriate content. This can potentially harm your personal and professional relationships.
2. Consequences of not prioritizing security
Failing to protect your online data can lead to serious consequences. Cybercriminals can use your personal information to commit identity theft, financial fraud, or even blackmail you. You could lose access to your online accounts or have your credit score damaged. In extreme cases, a data breach can result in lawsuits or criminal charges.
Not protecting your online data can also have a significant impact on your mental health. Constantly worrying about the security of your personal information can cause stress and anxiety. It can also damage your trust in others and negatively impact your relationships.
3. Choosing and using antivirus
Antivirus software is, up to today, one of the most effective ways to protect your devices and therefore your data. Antivirus software helps to prevent, detect, and remove malware from your devices. Malware is software specifically designed to invade your computer, access and steal your personal information, or ruin your files.
It is essential to select a reliable provider when opting for antivirus software. Everyone should look for providers with a track record of success in the cybersecurity industry. Also, make sure that the software is regularly updated to protect against the latest threats.
Once you’ve chosen your antivirus software, make sure to use it correctly. Keep the software up-to-date and run regular scans to check for any malware. Be careful when downloading files or clicking on links, and avoid suspicious websites.
4. The growing need for cybersecurity pros
As the need for cybersecurity increases, so does the demand for cybersecurity experts. Professionals specializing in protecting computer systems, networks, and data from cyber-attacks are known as cybersecurity experts. They are responsible for implementing security measures, detecting and preventing cyber threats, and responding to security incidents.
The outlook for skilled cybersecurity professionals is favorable, with a sustained demand projected in the foreseeable future. The growing importance of cybersecurity and the increasing need for professionals who specialize in protecting computer systems, networks, and data from cyber threats are the key drivers behind this trend. As a result, pursuing a career in cybersecurity can offer long-term job security and growth opportunities in a rapidly evolving industry.

5. Pursuing a career in cybersecurity
If you’re interested in a cybersecurity career, know that there are many paths you can take. You can start by obtaining a degree in computer science or a related field. Many universities offer cybersecurity specializations within their computer science programs.
In addition to obtaining a degree, it’s also important to gain practical experience. One should search for internships or entry-level positions in the cybersecurity field. Participating in internships or entry-level jobs within the cybersecurity field will enable you to acquire practical experience and enhance your skill set.
Another option is to obtain industry certifications. Certifications demonstrate your knowledge and skills in a specific area of cybersecurity.
6. Protecting Online Data: creating trust and Happiness
Protecting our online data not only helps to safeguard our identity and reputation, but it can also have a positive impact on our mental health. When we know that our personal information is secure, we can feel a sense of inner peace and security.
It can also help to build trust in your personal and professional relationships. When you take steps to protect your personal information, you demonstrate that you value your privacy and security. This can help build trust with those around you.
In addition, protecting your online data can lead to a sense of empowerment and happiness. When you take control of your digital life, you can feel a sense of accomplishment and pride. You can also enjoy the benefits of being able to use the internet with confidence and without fear of cyber attacks.
Conclusion
As technology continues to advance, protecting your online data is more important than ever. Cybercriminals are always looking for new ways to access your valuable personal information and the consequences of them achieving their goals can be so harmful that it is worth taking the time to implement security measures.
The time to protect your online data is now. By taking steps to protect your online data, such as using antivirus software and pursuing a career in cybersecurity, you can safeguard your identity and reputation, build trust in your relationships, and enjoy a sense of inner peace and happiness.
Cybersecurity experts, on the other hand, are the guardians of the virtual world, working tirelessly to protect sensitive data from cyber-attacks and ensuring that the internet is a reliable and efficient tool for everyone to use. By pursuing a career in cybersecurity, you can become an integral part of this community and contribute to creating a new digital world that is both safe and easy to navigate, enabling people to make the most of its endless possibilities while excluding negative experiences.
Blockchain
Perché Dobbiamo Utilizzare Un’Applicazione Antivirus Su Android?
Perché Dobbiamo Utilizzare Un’applicazione Antivirus Su Android? Rischi diversi, Vantaggi dell’utilizzo di applicazioni antivirus su Android

Una soluzione altrettanto fondamentale per garantire che il tuo dispositivo non venga infettato da questi programmi software malevoli (virus, trojan, adware, spyware) è il programma antivirus. Di conseguenza, il codice rileva e respinge anche l’app che può essere sviluppata in modo inefficiente dagli hacker. L’altra virtù è che può anche aiutare la tua macchina a essere sotto tiro e prevenire altri attacchi informatici da attacchi di phishing.
1. Rischi diversi
Android, essendo il sistema operativo mobile più utilizzato a livello globale, è diventato un obiettivo primario per i criminali informatici. Dal malware e ransomware agli attacchi di phishing e al furto di identità, le minacce sono diverse e in continua evoluzione. A differenza dei computer tradizionali, i dispositivi mobili spesso non dispongono delle solide misure di sicurezza inerenti ai sistemi operativi desktop, rendendoli suscettibili di sfruttamento.
a. Minaccia malware
Il malware, abbreviazione di software dannoso, comprende un ampio spettro di minacce progettate per infiltrarsi, interrompere o danneggiare un dispositivo o una rete. Nel regno di Android, i malware possono mascherarsi da applicazioni legittime, nascondersi negli app store o mascherarsi da download innocui dal web. Una volta installato, il malware può provocare danni rubando informazioni sensibili, spiando le attività degli utenti o addirittura rendendo il dispositivo inutilizzabile.
b. Insidie del phishing
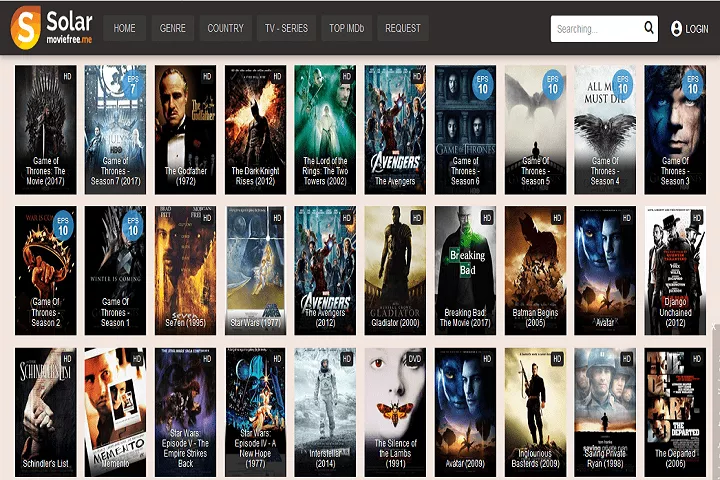
Gli attacchi di phishing, un’altra minaccia diffusa, mirano a indurre gli utenti a divulgare informazioni personali come password, numeri di carta di credito o credenziali di accesso. Questi attacchi spesso utilizzano tattiche di ingegneria sociale, sfruttando siti Web, e-mail o messaggi falsi per ingannare le vittime ignare. Con la comodità di accedere alla posta elettronica e navigare sul Web sui nostri dispositivi Android, il rischio di cadere preda di truffe di phishing diventa sempre presente.
2. Vantaggi dell’utilizzo di applicazioni antivirus su Android
a. Il ruolo delle applicazioni antivirus
Le applicazione antivirus gratuita per Android si rivelano indispensabili guardiani della nostra sicurezza digitale di fronte a queste minacce incombenti. Queste soluzioni software sono progettate specificamente per rilevare, prevenire ed eliminare programmi dannosi, rafforzando così le difese dei nostri dispositivi Android.
b. Protezione in tempo reale
Le applicazioni antivirus utilizzano algoritmi sofisticati e analisi euristiche per identificare e neutralizzare proattivamente le minacce in tempo reale. Monitorando continuamente le attività del dispositivo e i flussi di dati in entrata, questi strumenti fungono da sentinelle vigili, intercettando il malware prima che possa infiltrarsi nel sistema.
c. Scansione completa
Una delle funzioni principali delle applicazioni antivirus è l’esecuzione di scansioni complete della memoria, delle applicazioni e dei file del dispositivo. Attraverso tecniche di scansione approfondita, questi strumenti ispezionano meticolosamente ogni angolo del dispositivo, eliminando ogni traccia di malware o attività sospette. Eseguendo scansioni regolari, gli utenti possono garantire che i loro dispositivi Android rimangano liberi da minacce nascoste.
d. protezione della rete
In un’era in cui la navigazione sul Web è diventata parte integrante della nostra vita quotidiana, le applicazioni antivirus estendono il loro ombrello protettivo per comprendere le attività online. Integrando funzionalità di protezione Web, questi strumenti possono rilevare e bloccare siti Web dannosi, tentativi di phishing e altre minacce online in tempo reale. Che si tratti di fare acquisti, operazioni bancarie o semplicemente navigare sul Web alla ricerca di informazioni, gli utenti possono navigare nel panorama digitale con sicurezza, sapendo che la loro applicazione antivirus è al loro fianco.
e. Misure antifurto
Oltre a combattere malware e minacce online, molte applicazioni antivirus offrono funzionalità aggiuntive come funzionalità antifurto e generatore di password sicuro. In caso di smarrimento o furto del dispositivo, questi strumenti consentono agli utenti di localizzare, bloccare o cancellare da remoto il proprio dispositivo Android, proteggendo i dati sensibili dalla caduta nelle mani sbagliate. Grazie alla possibilità di tracciare la posizione del dispositivo o attivare un allarme da remoto, gli utenti possono mitigare le potenziali conseguenze del furto o dello smarrimento del dispositivo.
f. Reputazione e affidabilità
Quando si valutano le applicazioni antivirus, è essenziale considerare la reputazione e il track record dello sviluppatore del software. Scegli marchi affermati con una comprovata storia nella fornitura di soluzioni di sicurezza affidabili e aggiornamenti tempestivi. Leggere recensioni e testimonianze di altri utenti può fornire preziose informazioni sull’efficacia e sulle prestazioni dell’applicazione antivirus.
g. Impatto sulle prestazioni
Sebbene le applicazioni antivirus svolgano un ruolo cruciale nella protezione del tuo dispositivo Android, non dovrebbero andare a scapito delle prestazioni o della durata della batteria. Scegli soluzioni leggere e ottimizzate che riducono al minimo il consumo di risorse e funzionano perfettamente in background. Evita applicazioni eccessive che consumano le risorse di sistema o causano rallentamenti, poiché possono compromettere l’esperienza dell’utente.
Conclusione
Le applicazioni antivirus fungono da guardiani indispensabili, proteggendo la nostra oasi digitale da malware, attacchi di phishing e altre attività nefaste. Protezione Web e misure antifurto: questi strumenti consentono agli utenti di navigare nel panorama digitale con sicurezza e tranquillità. Mentre abbracciamo le infinite possibilità offerte dai nostri dispositivi Android, non dimentichiamoci di rafforzare le loro difese con l’armatura della protezione antivirus.

 Instagram3 years ago
Instagram3 years agoBuy IG likes and buy organic Instagram followers: where to buy them and how?

 Instagram3 years ago
Instagram3 years ago100% Genuine Instagram Followers & Likes with Guaranteed Tool

 Business4 years ago
Business4 years ago7 Must Have Digital Marketing Tools For Your Small Businesses

 Instagram3 years ago
Instagram3 years agoInstagram Followers And Likes – Online Social Media Platform