Software
How To Fix Corrupt JPEG File Signature?
How to fix corrupt jpeg file signature?. Some tools can help repair and restore JPEG images that become inaccessible due to corrupt JPEG file signature or title.

If you cannot open or preview JPEG image files, chances are, its file signature is corrupt. A file signature contains unique data in bytes on a file header that verifies the file content and its type. Most cameras save image data in the file header. If this file information gets corrupt, you won’t be able to access or read that file. Your image file may also throw errors like ‘invalid format’ or ‘can’t open this file.’
So is it possible to recover such photos that have corrupt JPEG file signature or header?
Yes, thankfully, you can if the image file header is not overwritten. Some tools can help repair and restore JPEG images that become inaccessible due to corrupt JPEG file signature or title.
Why JPEG file signature gets corrupt?
JPEG file header can get corrupted due to many reasons. Maybe your photos storage drive or removable media has bad sectors. A virus attack in your system can also damage the file header. Further, incomplete photo transfer, sudden interruption during a file download, etc., can corrupt JPEG file signature, making your photos unreadable.
How to repair corrupt JPEG file signature?
You can repair the JPEG file header and signature using any Hex Editor or photo repair software. These tools can change or fix the corrupt file header making your photos accessible.
Table of Contents
1. Repair corrupt JPEG file header with Hex Editor tool
Hex editor program displays the raw binary data of a JPEG file. You should be familiar with hexadecimal to fix damaged JPEG file signature by using this method.
To repair a corrupt JPEG file with Hex editor, you require a healthy JPEG photo captured from the same device as your corrupt file. The tool lets you view and compare binary data of both the JPEG pictures. Based on your observations, you can edit and fix the corrupt JPEG file header in Hex editor. It’s important to note that if binary data is missing in Hex Editor, i.e., showing 0 bytes, and you cannot repair that JPEG file.
Just in fact, if you do not have a healthy JPEG file to compare in Hex Editor, create one using Windows MS Paint by following the below steps:
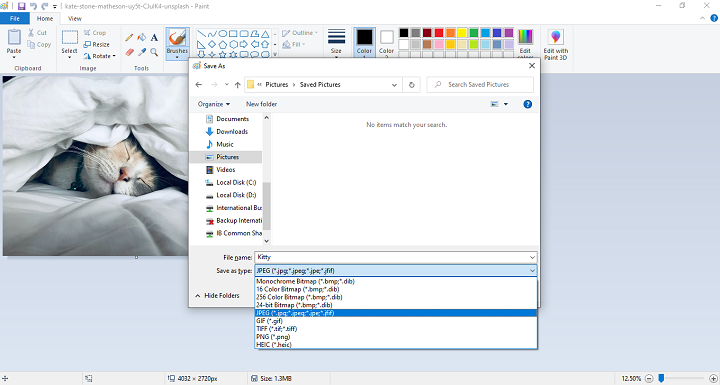
- Open MS Paint on your Windows PC.
- Draw anything in the black space.
- In the top menu bar, click on File followed by Save As.
- Select JPEG picture, enter the file name and location to save the new file.
- Click Save.
You can use this new JPEG file to compare raw data with the corrupted file in the Hex Editor software.
Hex Editors are available for Windows, Mac, and Linux machines. Some commonly used Hex Editors are Hex Fiend, OxED, and Neo.
2. Repair corrupt JPEG files signature with a photo repair software
Another efficient way to repair JPEG file signature or header is by using professional photo repair software. The software is designed to automatically fix corrupt JPEG file header and data once the image file is imported. Unlike Hex Editor, it doesn’t require any technical know-how. It is quick and can repair multiple JPEG files at a time. You can easily find many JPEG photo repair software online but make sure to download a trusted tool free from viruses or malware.
Here we suggest a popularly used JPEG repair software, Stellar Repair for Photo.
It has a simple image repair process. Add a file, click on the ‘repair’ button, and let the software do its task. The software also shows the preview of the repaired picture before saving it at your chosen drive location.
Stellar Repair for Photo caters to both Windows and Mac users. Further, you can repair raw image file formats used in cameras from Nikon, Canon, Olympus, Sony, etc.
3. Restore the correct JPEG file from backup
Back up essential photos is a significant relief in case your files are corrupted. You don’t need to fret over the lost photos and try repairing corrupt image files. Just quickly restore the lost or corrupted JPEG photos from the backup folder.
4. To Sum Up
It is an awful feeling to find your JPEG photos inaccessible due to file corruption. The situation is more troublesome when you don’t have a backup of your precious pictures. Hex Editor tools can repair corrupt file signature or header but are cumbersome to use. You ought to have proficiency in hexadecimal or binary data in files to use the program.
On the other hand, professional JPEG repair software is user-friendly. No prior knowledge is required. It is fast and can repair JPEG file signature, header, or data corruption in no time, making your pictures as vivid as before.
-

 Instagram5 years ago
Instagram5 years agoBuy IG likes and buy organic Instagram followers: where to buy them and how?
-

 Instagram5 years ago
Instagram5 years ago100% Genuine Instagram Followers & Likes with Guaranteed Tool
-

 Business6 years ago
Business6 years ago7 Must Have Digital Marketing Tools For Your Small Businesses
-

 Instagram5 years ago
Instagram5 years agoInstagram Followers And Likes – Online Social Media Platform














